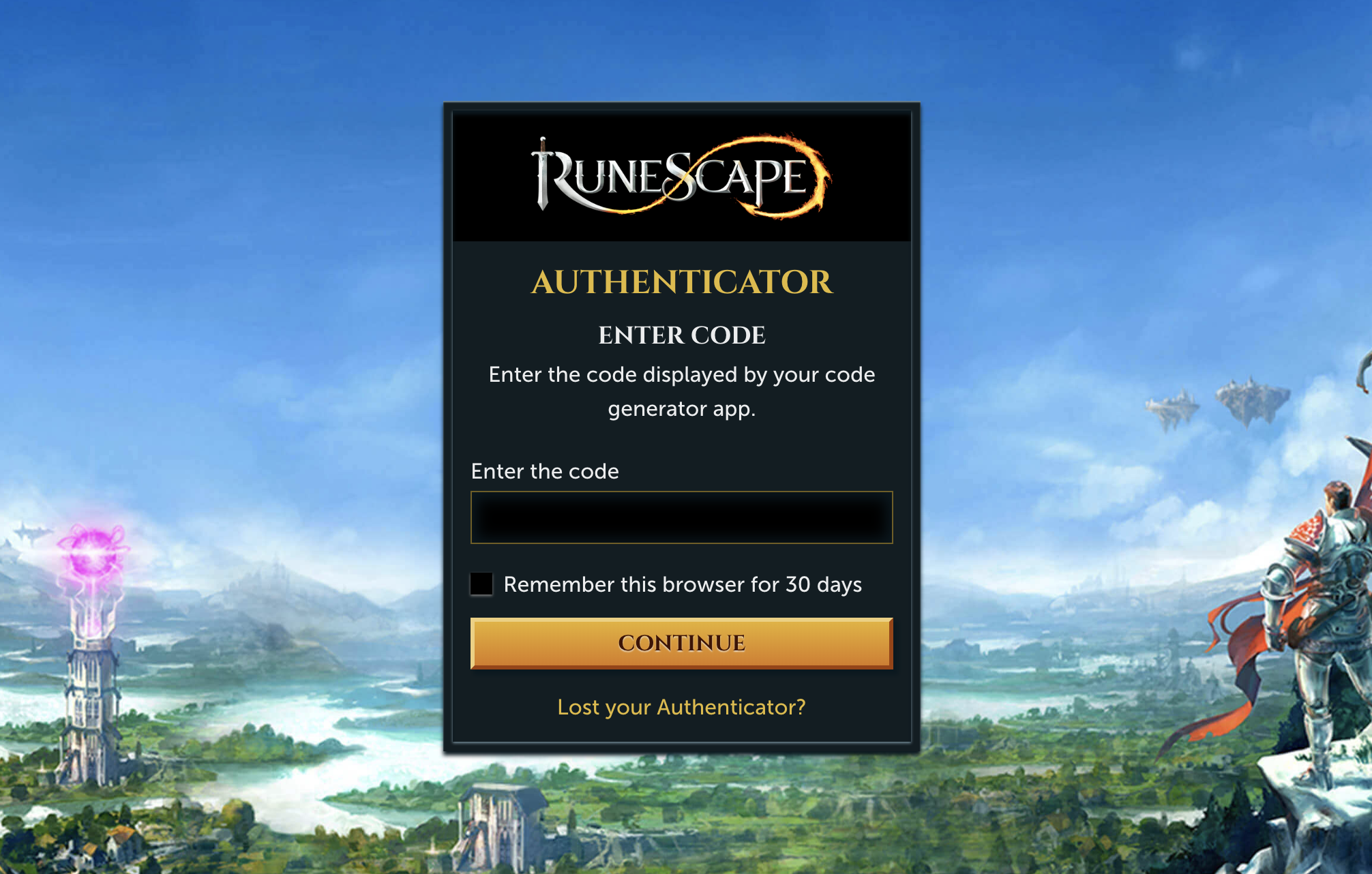
I introduced two-factor authentication (2FA) to the RuneScape website. Prior to this it had only existed in the RuneScape game clients, which presented an attack vector for malicious entities with access to the target’s email – they could bypass the games’ checks using the website and disable the 2FA integration. This came at a time when we had promised security improvements to players as part of an overarching project to prevent accounts from being compromised.
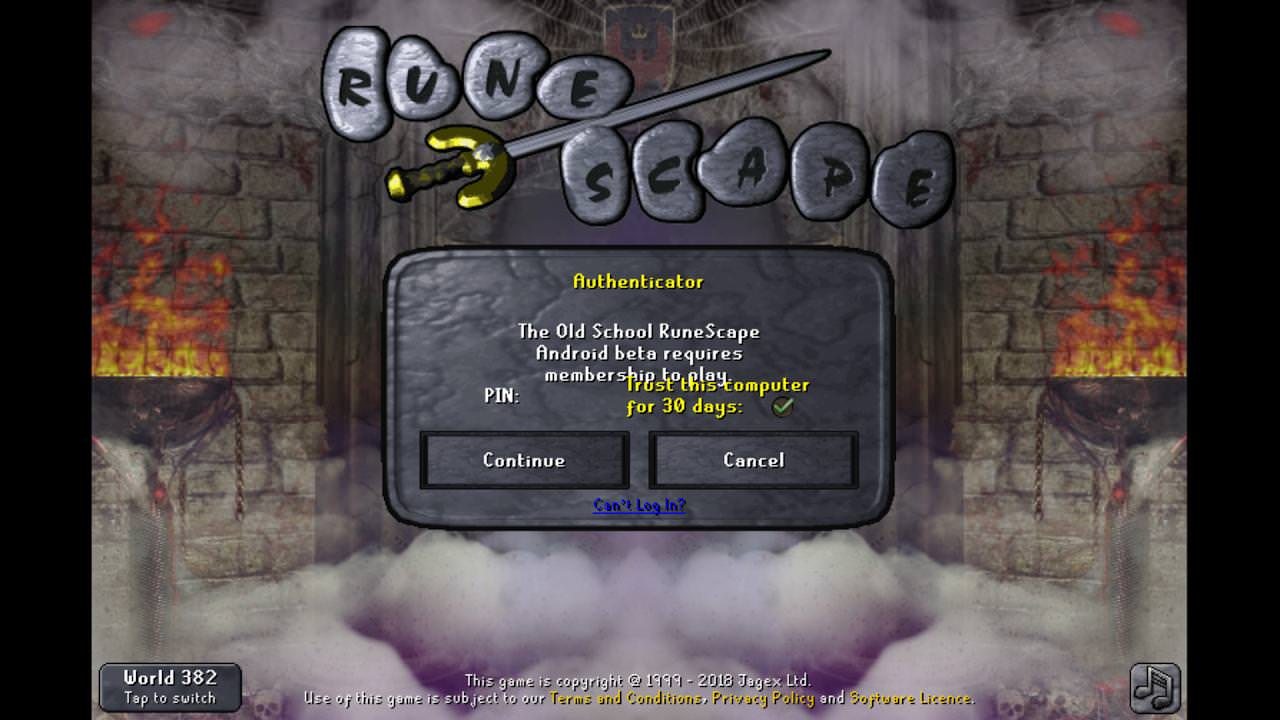
I helped implement this in the website log-in flow – a typical six-digit pin check for accounts with 2FA enabled. This required careful consideration of security implications – we needed to ensure we were not creating another vulnerability by providing automated attacks with more information about a player’s account. We needed to create a short-lived session for users who had successfully logged in using their username and password, but had yet to input their 2FA code; the user may accidentally close their browser, tab, or simply refresh. Ultimately, we balanced an un-intrusive and familiar web paradigm against risk mitigation, and produced something simple and effective that incurred a positive sentiment boost.
I gained experience:
- Implementing caching mechanisms to websites
- Implementing code-based 2FA
- Creating front-end templates

